Hunt Library Maximum Sessions Reached
Earlier attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and institute the correct places to point their scope at, they'll utilise a web server scanning tool such as Nikto for hunting down vulnerabilities that could exist potential attack vectors.
Nikto is a uncomplicated, open-source spider web server scanner that examines a website and reports back vulnerabilities that it found which could exist used to exploit or hack the site. Likewise, it's one of the nearly widely used website vulnerabilities tools in the manufacture, and in many circles, considered the industry standard.
Although this tool is extremely effective, it'southward not stealthy at all. Any site with an intrusion-detection system or other security measures in place will find that it'southward existence scanned. Initially designed for security testing, stealth was never a business.
- Don't Miss: Utilise Metasploit's WMAP to Scan Web Apps for Vulnerabilities
The Right Way to Use Nikto
If you merely run Nikto past itself on a targeted website, you may not know what to exercise with the information from the browse. Nikto is actually more similar a laser pointer to telephone call in a much larger strike, and you'll see how that plays out in a little bit.
Get-go, permit's talk most the target surface. This is pretty much anywhere a hacker will attempt to attack and could include things such as network-exposed printers and a spider web server. When we get to using Nikto later, we'll need to provide it with 1 of three dissimilar types of data: an IP address for a local service, a spider web domain to attack, or an SSL/HTTPS website.
Before diving correct into a browse with Nikto, it'southward meliorate to exercise some boosted reconnaissance using an open-source intelligence tool such as Maltego. Tools similar this tin help build a profile and a more focused list of available targets that should be concentrated on. Once that'southward washed, Nikto can be used to hone in on potential vulnerabilities for targets on the list.
- Don't Miss: How to Use Maltego to Fingerprint an Entire Network
If lucky, a vulnerability with a weaponized exploit will be found, meaning there's a tool out there already to have advantage of the weakness. With the advisable tool, which will automatically exploit the vulnerability, a hacker tin can gain access to the target to perform any number of backside-the-scenes attacks, similar adding code to perform a malicious activity.
Step 1: Install Nikto
If you're running Kali Linux, Nikto comes preinstalled, so you don't accept to download or install anything. It'll exist located in the "Vulnerability Assay" category. If yous don't have information technology for some reason, you can go Nikto from its GitHub or just use the apt install command.
apt install nikto If you're doing this on a Mac, you can use Homebrew to install Nikto.
brew install nikto Step two: Go to Know Nikto
Before you dive into scanning web servers with Nikto, lets y'all employ the -Assistance option to see everything that can be done inside Nikto.
nikto -Assistance Options: -inquire+ Whether to ask virtually submitting updates yes Ask virtually each (default) no Don't ask, don't send motorcar Don't inquire, just send -Cgidirs+ Scan these CGI dirs: "none", "all", or values similar "/cgi/ /cgi-a/" -config+ Employ this config file -Display+ Plow on/off display outputs: 1 Evidence redirects 2 Show cookies received 3 Show all 200/OK responses four Show URLs which crave hallmark D Debug output E Display all HTTP errors P Print progress to STDOUT S Scrub output of IPs and hostnames V Verbose output -dbcheck Cheque database and other key files for syntax errors -evasion+ Encoding technique: 1 Random URI encoding (not-UTF8) 2 Directory self-reference (/./) iii Premature URL catastrophe 4 Prepend long random string 5 Fake parameter half-dozen TAB as request spacer vii Change the case of the URL 8 Utilize Windows directory separator (\) A Use a carriage return (0x0d) every bit a request spacer B Use binary value 0x0b as a request spacer -Format+ Save file (-o) format: csv Comma-separated-value htm HTML Format nbe Nessus NBE format sql Generic SQL (meet docs for schema) txt Plain text xml XML Format (if non specified the format will exist taken from the file extension passed to -output) -Assist Extended help information -host+ Target host -404code Ignore these HTTP codes every bit negative responses (always). Format is "302,301". -404string Ignore this string in response body content every bit negative response (e'er). Tin exist a regular expression. -id+ Host authentication to use, format is id:pass or id:pass:realm -primal+ Client certificate key file -list-plugins List all bachelor plugins, perform no testing -maxtime+ Maximum testing time per host (e.thousand., 1h, 60m, 3600s) -mutate+ Approximate additional file names: ane Test all files with all root directories ii Gauge for password file names 3 Enumerate user names via Apache (/~user blazon requests) 4 Enumerate user names via cgiwrap (/cgi-bin/cgiwrap/~user type requests) 5 Endeavor to beast forcefulness sub-domain names, assume that the host name is the parent domain half-dozen Endeavor to judge directory names from the supplied dictionary file -mutate-options Provide information for mutates -nointeractive Disables interactive features -nolookup Disables DNS lookups -nossl Disables the use of SSL -no404 Disables nikto attempting to guess a 404 page -Option Over-ride an option in nikto.conf, can exist issued multiple times -output+ Write output to this file ('.' for car-name) -Pause+ Intermission between tests (seconds, integer or float) -Plugins+ List of plugins to run (default: ALL) -port+ Port to apply (default 80) -RSAcert+ Customer document file -root+ Prepend root value to all requests, format is /directory -Salvage Save positive responses to this directory ('.' for automobile-proper noun) -ssl Force ssl mode on port -Tuning+ Browse tuning: one Interesting File / Seen in logs two Misconfiguration / Default File iii Information Disclosure 4 Injection (XSS/Script/HTML) 5 Remote File Retrieval - Inside Web Root half dozen Denial of Service 7 Remote File Retrieval - Server Broad 8 Command Execution / Remote Shell 9 SQL Injection 0 File Upload a Authentication Featherbed b Software Identification c Remote Source Inclusion d WebService e Administrative Console x Reverse Tuning Options (i.e., include all except specified) -timeout+ Timeout for requests (default 10 seconds) -Userdbs Load only user databases, non the standard databases all Disable standard dbs and load but user dbs tests Disable only db_tests and load udb_tests -useragent Over-rides the default useragent -until Run until the specified time or elapsing -update Update databases and plugins from CIRT.net -useproxy Utilize the proxy divers in nikto.conf, or argument http://server:port -Version Print plugin and database versions -vhost+ Virtual host (for Host header) + requires a value Step 3: Use the Basic Syntax
As you can run into from the previous step, Nikto has many options, merely for our purposes, we'll stick to the bones syntax as follows. Nosotros'll substitute the <IP or hostname> with the actual IP address or hostname sans angle brackets.
nikto -h <IP or hostname> Notwithstanding, Nikto is capable of doing a scan that can go afterwards SSL and port 443, the port that HTTPS websites utilize (HTTP uses port 80 by default). And so nosotros're not just limited to scanning old sites, we can practice vulnerability assessments on sites that use SSL, which is pretty much a requirement these days to be indexed in search results.
If nosotros know it's an SSL site that we're targeting, we tin specify it in Nikto to save some fourth dimension on the browse by adding -ssl to the finish of the control.
nikto -h <IP or hostname> -ssl Footstep 4: Browse an SSL-Enabled Website
For example, let'south start with scanning pbs.org to come across some of the types of information that a Nikto scan will show. Afterwards it connects to port 443, we see that there'due south some useful information nigh the goose egg and a listing of other details similar that the server is Nginx, only there's non a whole lot of interesting information here for us.
nikto -h pbs.org -ssl - Nikto v2.i.vi ------------------------------------------------------------------------------ - STATUS: Starting up! + Target IP: 54.225.198.196 + Target Hostname: pbs.org + Traget Port: 443 ------------------------------------------------------------------------------ + SSl Info: Subject field: /CN=world wide web.pbs.org Altnames: account.pbs.org, admin.pgs.org, dipsy-tc.pbs.org, docs.pbs.org, ga.video.cdn.pbs.org, git.pbs.org, heart.ops.pbs.org, hub-dev.pbs.org, image.pbs.org, jaws..pbs.org, kids.pbs.org, koth-qa.svp.pbs.org, login.pbs.org, ops.pbs.org, pbs.org, thespian.pbs.org, projects.pbs.org, sentry.pbs.org, teacherline.pbs.org, urs.pbs.org, video.pbs.org, weta-qa.svp.pbs.org, whut-qa.svp.pbs.org, wnet.video-qa.pbs.org, wnet.video-staging.pbs.org, www-cache.pbs.org, www.pbs.org Ciphers: ECDHE-RSA-AES128-GCM-SHA256 Issuer: /C-US/0=Let'south Encrypt/CN=Permit's Encrypt Dominance X3 + Commencement Fourth dimension: 2018-12-05 23:34:06 (GMT-eight) ------------------------------------------------------------------------------ + Server: nginx + The anti-clickjacking X-Frame-Options header is not present. + The X-XSS-Protection header is not defined. This header can hint to the user agent to protect against some forms of XSS + Uncommon header 'x-pbs-fwsrvname' found, with contents: fwcacheproxy1 + The site uses SSL and the Strict-Transport-Security HTTP header is not defined. + The 10-Content-Blazon-Options header is not prepare. This could allow the user amanuensis to render the content of the site in a different fashion to the MIME type + Root page / redirects to: https://www.pbs.org/ + No CGI Directories found (employ '-C all' to force check all possible dirs) + RC-1918 IP address found in the 'x-pbs-appsvrip' header: The IP is "10.137.181.52". + Uncommon header 'x-cache-fs-condition' establish, with contents: EXPIRED + Uncommon header 'x-pbs-appsvrname' plant, with contents: fwcacheproxy1 + Uncommon header 'x-pbs-appsvrip' found, with contents: ten.137.181.52 + Server leaks inodes via ETags, header plant with file /pbs.org.aught, fields: 0x5b96537e 0x1678 + 7446 requests: 0 error(s) and x item(s) reported on remote host + Cease Time: 2018-12-06 00:30:29 (GMT-viii) (3383 seconds) ------------------------------------------------------------------------------ + 1 host(due south) tested Step v: Scan an IP Accost
Now that we performed a quick scan of a website, let's effort using Nikto on a local network to find embedded servers such as a login page for a router or an HTTP service on another machine that'southward only a server with no website. To become started, allow's notice our IP address using ifconfig.
ifconfig en0: flags=8863<UP,Broadcast,SMART,RUNNING,SIMPLEX,MULTICAST> mtu 1500 inet 192.168.0.48 netmask 0xffffff00 circulate 192.168.0.255 inet6 XXXX::Xxx:XXXX:XXXX:XXXX%en0 prefixlen 64 secured scopeid 0x8 ether XX:20:Twenty:XX:XX:XX txqueuelen 1000 (Ethernet) inet6 XXXX::XXX:XXXX:XXXX:XXXX%en0 prefixlen 64 autoconf secured inet6 XXXX::Xxx:XXXX:XXXX:XXXX%en0 prefixlen 64 autoconf temporary nd6 options=201<PERFORMNUD,DAD> media: autoselect status: active en2: flags=8863<UP,Circulate,SMART,RUNNING,PROMISC,SIMPLEX,MULTICAST> mtu 1500 options=60<TS04,TS06> ether XX:XX:Xx:Twenty:XX:XX media: autoselect <full-duplex> status: inactive The IP accost we want is the "inet" one. So nosotros can run ipcalc on information technology to get our network range. If you don't have ipcalc, y'all tin install it with apt install ipcalc, then effort once again. The range will be next to "Network," in my case, 192.168.0.0/24.
ipcalc 192.168.0.48 Address: 192.168.0.48 11000000.10101000.00000000. 00110000 Netmask: 255.255.255.0 = 24 11111111.11111111.11111111. 00000000 Wildcard: 0.0.0.255 00000000.00000000.00000000. 11111111 => Network: 192.168.0.0/24 11000000.10101000.00000000. 00000000 HostMin: 192.168.0.1 11000000.10101000.00000000. 00000001 HostMax: 192.168.0.254 11000000.10101000.00000000. 11111110 Broadcast: 192.168.0.255 11000000.10101000.00000000. 11111111 Hosts/Net: 254 Class C, Private Cyberspace Now, nosotros're going to want to run Nmap to find services running in the network range. Let's scan port 80 with our range and tack on -oG (grepable output) to extract only the hosts that are upward and running, i.e., the ones responding indicating that port lxxx is open. Then we'll save everything to a file, which I'chiliad naming nullbyte.txt, just could be named anything.
nmap -p 80 192.168.0.0/24 -oG nullbyte.txt Starting Nmap seven.60 ( https://nmap.org ) at 2018-12-06 00:43 PST Nmap scan report for 192.168.0.i Host is up (0.021s latency). PORT STATE SERVICE 80/tcp open up http Nmap scan study for 192.168.0.2 Host is up (0.088s latency). PORT STATE SERVICE 80/tcp open http Nmap browse report for 192.168.0.4 Host is up (0.032s latency). PORT Land SERVICE 80/tcp open up http Nmap browse study for 192.168.0.five Host is up (0.020s latency). PORT STATE SERVICE fourscore/tcp open up http Nmap scan report for 192.168.0.11 Host is up (0.068s latency). PORT STATE SERVICE lxxx/tcp airtight http Nmap scan written report for 192.168.0.24 Host is up (0.023s latency). PORT Country SERVICE fourscore/tcp closed http Nmap scan written report for 192.168.0.31 Host is up (0.059s latency). PORT STATE SERVICE 80/tcp airtight http Nmap scan report for 192.168.0.48 Host is up (0.030s latency). PORT STATE SERVICE eighty/tcp closed http Nmap scan report for 192.168.0.lx Host is upwards (0.092s latency). PORT State SERVICE 80/tcp closed http Nmap done: 256 IP addresses (nine hosts upward) scanned in 8.92 seconds There's a nice little trick that tin can send all the up hosts directly to Nikto for scanning. We use cat to read the output stored in our nullbyte.txt document (or whatsoever you named it). Then, there's awk, a Linux tool that will help search for the following blueprint, where Up means the host is upward and impress $2 means to print out the second word in that line for each, i.e., just the IP address. Then, we send that data to a new file called targetIP.txt (or whatever you'd like to name it).
cat nullbyte.txt | awk '/Up$/{impress $2}' | cat >> targetIP.txt We tin can at present view the contents of our new file with cat to run into all the IP addresses that have port 80 open up.
true cat targetIP.txt 192.168.0.1 192.168.0.ii 192.168.0.4 192.168.0.5 192.168.0.eleven 192.168.0.24 192.168.0.31 192.168.0.48 192.168.0.60 This is perfect for Nikto because it can hands translate files like this. And then we can send this output over to Nikto with the following command.
nikto -h targetIP.txt The results volition look similar to the ones we got when performing the SSL scan.
Step 6: Browse an HTTP Website
Nosotros've scanned a secure website and an IP address on a local network, and now information technology'due south time to go after an unsecured web domain using port 80. For this example, I'thou using "afl.com.au,' which was not using SSL at the time I performed this browse.
nikto -h www.afl.com.au - Nikto v2.1.6 --------------------------------------------------------------------------- + Target IP: 159.180.84.10 + Target Hostname: www.afl.com.au + Target Port: fourscore + Start Time: 2018-12-05 21:48:32 (GMT-8) --------------------------------------------------------------------------- + Server: instart/nginx + Retried via header: i.1 varnish (Varnish/6.one), 1.1 e9ba0a9a729ff2960a04323bf1833df8.cloudfront.net (CloudFront) + The anti-clickjacking X-Frame-Options header is non nowadays. + The X-XSS-Protection header is non defined. This header can hint to the user agent to protect against some forms of XSS + Uncommon header 'ten-cache' found, with contents: Miss from cloudfront + Uncommon header 'x-instart-cache-id' found, with contents: 17:12768802731504004780::1544075250 + Uncommon header 'five-enshroud-hit' constitute, with contents: Hit + Uncommon header 'x-amz-cf-id' found, with contents: Dr-r6OwO5kk9ABt4ejzpc7R7AIF6SuH6kfJHQgP0v6xZoHwMLE55rQ== + Uncommon header 'ten-instart-request-id' found, with contents: 12814413144077601501:BEQ01-CPVNPPRY18:1552504721:0 + Uncommon header 'x-oneagent-js-injection' found, with contents: true + Uncommon header 'grace' found, with contents: cache + The X-Content-Type-Options header is not set. This could allow the user agent to render the content of the site in a different mode to the MIME blazon + Uncommon header 'x-ruxit-js-amanuensis' found, with contents: true + Cookie dtCookie created without the httponly flag + Server banner has inverse from 'instart/nginx' to 'nginx' which may suggest a WAF, load balancer or proxy is in place + No CGI Directories found (use '-C all' to force check all possible dirs) + Entry '/sites/' in robots.txt returned a non-forbidden or redirect HTTP code (200) + Entry '/search/' in robots.txt returned a non-forbidden or redirect HTTP lawmaking (200) + Entry '*.mobileapp' in robots.txt returned a non-forbidden or redirect HTTP lawmaking (400) + Entry '*.liveradio' in robots.txt returned a non-forbidden or redirect HTTP code (400) + Entry '*.smartmobile' in robots.txt returned a non-forbidden or redirect HTTP lawmaking (400) + Entry '*.responsive' in robots.txt returned a non-forbidden or redirect HTTP code (400) + Entry '/stats?*/' in robots.txt returned a not-forbidden or redirect HTTP lawmaking (200) + "robots.txt" contains 8 entries which should be manually viewed. + OSVDB-3092: /sitemap.xml: This gives a nice listing of the site content. + OSVDB-3092: /psql_history: This might be interesting... + OSVDB-3092: /global/: This might be interesting... + OSVDB-3092: /home/: This might be interesting... + OSVDB-3092: /news: This might be interesting... + OSVDB-3092: /search.vts: This might be interesting... + OSVDB-3092: /stats.htm: This might be interesting... + OSVDB-3092: /stats.txt: This might be interesting... + OSVDB-3092: /stats/: This might exist interesting... + OSVDB-3092: /Stats/: This might exist interesting... + OSVDB-3093: /.wwwacl: Contains authorization information + OSVDB-3093: /.www_acl: Contains potency information + OSVDB-3093: /.htpasswd: Contains authorization information + OSVDB-3093: /.admission: Contains potency data + OSVDB-3093: /.addressbook: Pine addressbook, may store sensitive electronic mail address contact data and notes + OSVDB-3093: /.bashrc: User home dir was found with a trounce rc file. This may reveal file and path information. + OSVDB-3093: /.bash_history: A user's home directory may be set up to the web root, the crush history was retrieved. This should not exist accessible via the web. + OSVDB-3093: /.forward: User domicile dir was plant with a post forward file. May reveal where the user's mail is existence forwarded to. + OSVDB-3093: /.history: A user'south home directory may exist gear up to the web root, the shell history was retrieved. This should not be accessible via the web. + OSVDB-3093: /.htaccess: Contains configuration and/or authorization information + OSVDB-3093: /.lynx_cookies: User home dir found with LYNX cookie file. May reveal cookies received from arbitrary spider web sites. + OSVDB-3093: /.mysql_history: Database SQL? + OSVDB-3093: /.passwd: Contains potency information + OSVDB-3093: /.pinerc: User home dir plant with a PINE rc file. May reveal system information, directories and more than. + OSVDB-3093: /.plan: User domicile dir with a .plan, a now mostly outdated file for delivering data via the finger protocol + OSVDB-3093: /.proclog: User home dir with a Procmail rc file. May reveal mail traffic, directories and more than. + OSVDB-3093: /.procmailrc: User home dir with a Procmail rc file. May reveal subdirectories, mail contacts and more. + OSVDB-3093: /.profile: User abode dir with a shell profile was found. May reveal directory data and organization configuration. + OSVDB-3093: /.rhosts: A user'southward home directory may be ready to the web root, a .rhosts file was retrieved. This should not be accessible via the spider web. + OSVDB-3093: /.sh_history: A user'south home directory may be gear up to the web root, the shell history was retrieved. This should not be accessible via the web. + OSVDB-3093: /.ssh: A user's home directory may be set to the web root, an ssh file was retrieved. This should not exist attainable via the web. + OSVDB-5709: /.nsconfig: Contains authorization data + /portal/changelog: Vignette richtext HTML editor changelog found. + 7587 requests: 4 mistake(s) and 55 detail(s) reported on remote host + End Time: 2018-12-05 22:42:41 (GMT-8) (3249 seconds) --------------------------------------------------------------------------- + ane host(s) tested Above, nosotros can see that there's a Varnish server and some headers that help indicate how the website is configured. Notwithstanding, the juicier stuff is the directories found which can help snag configuration files that may comprise credentials or other things that take been misconfigured and left unintentionally accessible.
The items with the OSVDB prefix are vulnerabilities reported in the Open Source Vulnerability Database (a site that shut downward in 2016). Information technology's like to other vulnerability databases such equally SecurityFocus, Microsoft'due south Technet, and Mutual Vulnerabilities and Exposures. I prefer to check out the National Vulnerability Database.
While at that place aren't any major things that tin can be exploited from this browse, if at that place was, yous tin utilize the CVE reference tool to translate the OSVDB identifier to a CVE entry, and then you tin can employ i of the other sites in a higher place to read more nearly the vulnerability.
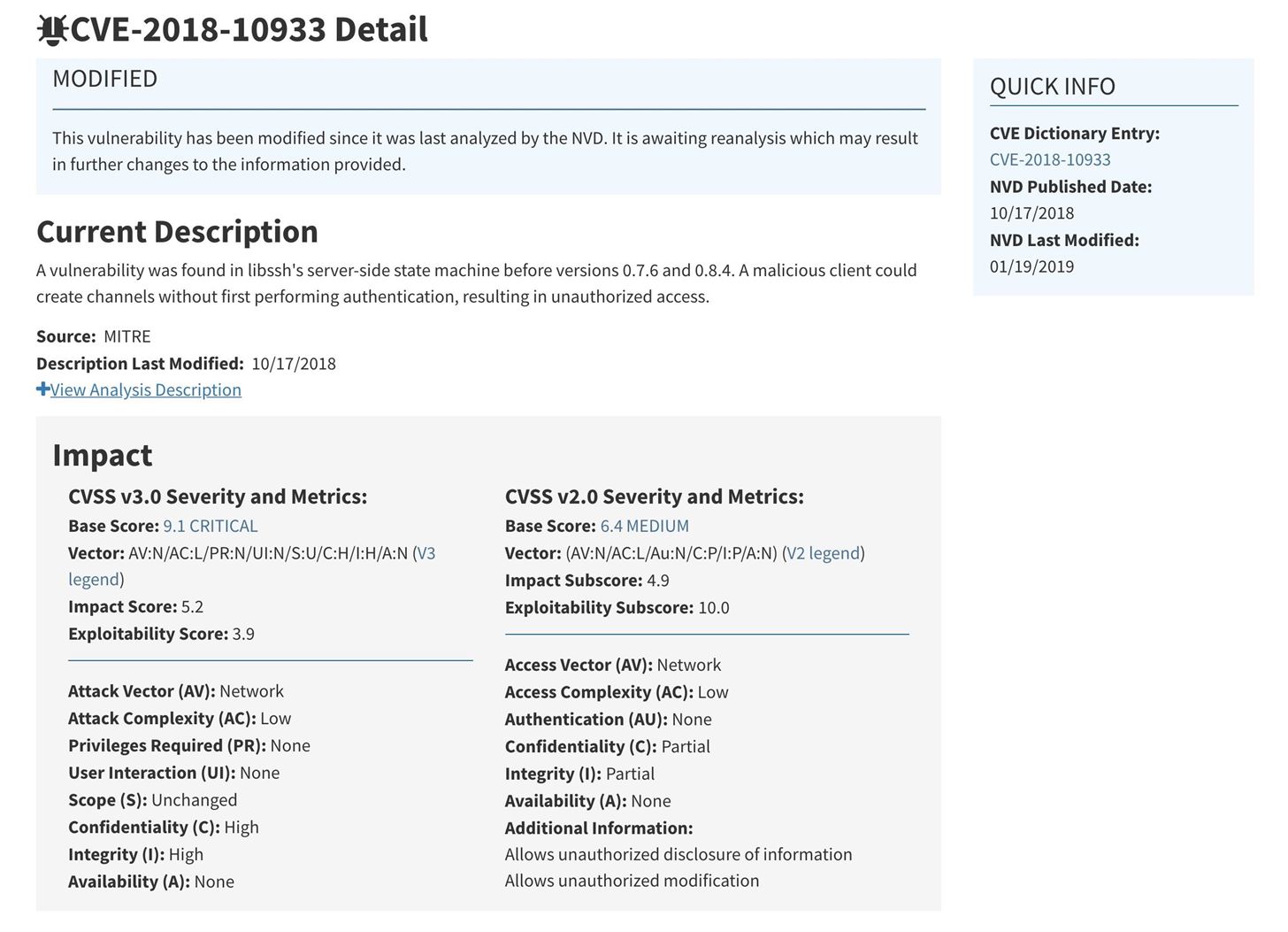
Permit'due south say we institute some worth exploring, such as CVE-2018-10933, a Libssh vulnerability we covered in item previously. The CVE holds data about what can exist exploited, what the severity score is (such every bit disquisitional), and some other information that can help determine an attack vector. If it something worth using, you can search Metasploit, as someone has already probable developed a weaponized module for it to exploit information technology more hands.
Step seven: Pair Scans with Metasploit
1 of the best things about Nikto is that y'all can actually export information into a format that Metasploit can read when you're performing a browse. To do, merely apply the commands to a higher place to perform the browse, but appending -Format msf+ to the end of it. The format can assistance the states quickly pair information retrieved with a weaponized exploit.
nikto -h <IP or hostname> -Format msf+ So, in this guide, we went from determining the target'due south surface area to finding a vulnerability and then pairing information technology with a weaponized exploit so we don't have to practice all of the piece of work. Since Nikto is not a stealthy tool, it's wise to perform these types of scans from a VPN, through Tor, or another type of service so that your existent IP address is not flagged for suspicious behavior.
Desire to first making money as a white chapeau hacker? Jump-first your hacking career with our 2020 Premium Ethical Hacking Certification Training Bundle from the new Null Byte Store and go over threescore hours of training from cybersecurity professionals.
Buy Now (xc% off) >
Other worthwhile deals to cheque out:
- 97% off The Ultimate 2021 White Chapeau Hacker Certification Bundle
- 99% off The 2021 All-in-1 Data Scientist Mega Bundle
- 98% off The 2021 Premium Learn To Code Certification Parcel
- 62% off MindMaster Mind Mapping Software: Perpetual License
Hunt Library Maximum Sessions Reached
Source: https://null-byte.wonderhowto.com/how-to/scan-for-vulnerabilities-any-website-using-nikto-0151729/
0 Response to "Hunt Library Maximum Sessions Reached"
Post a Comment